Half-life Deathmatch- Source Activation Crack -
More importantly, it proves a counterintuitive theorem of digital security: The crack is frozen, self-contained, and asks for no permissions. The official client is a living binary that decays as Steam’s API updates.
| Crack Version | Valve Counter-Measure | What it Revealed | | :--- | :--- | :--- | | engine.dll patch | Steam’s “Ultrascope” CRC check on engine.dll | That client-side authority is a myth; server trust is all that matters. | | Ticket replay | Dynamic ticket nonces (timestamp checks) | That Steam tickets had no hardware binding until 2009. | | Listmaster spoof | Forced server-side challenge-response (2011 update) | That Valve assumed the master server was the single source of truth. |
Abstract This paper examines the socio-technical phenomenon known colloquially as the “Half-Life Deathmatch: Source (HL2:DM) Activation Crack.” Rather than a simple piece of piracy software, this artifact represents a unique intersection of digital rights management (DRM) history, network protocol manipulation, and post-hoc game preservation. By analyzing the executable patches released between 2006 and 2010, this paper argues that the HL2:DM crack is not merely a tool for theft but a “phantom protocol”—a reverse-engineered key that inadvertently documented the shift from optional CD keys to mandatory, always-online Steam authentication. 1. Introduction: The Orange Box’s Shadow Released in 2006, Half-Life 2: Deathmatch was more than a multiplayer shooter; it was a stress test for Valve’s Steamworks API. Unlike its predecessor (the original Half-Life Deathmatch ), HL2:DM had no offline mode. It required a persistent connection to Steam’s authentication servers to even launch. This created a digital ghost: millions of copies of the game existed on physical CDs (from The Orange Box or HL2 Silver/Gold packages), but the activation server was a live, mutable gatekeeper.
Ultimately, the HL2:DM crack is not a hacker’s triumph or a pirate’s shame. It is a —ugly, illegal, and absolutely necessary for the archaeological recovery of early 2000s Source Engine multiplayer.
; Redirect master server DNS push offset szHostname ; "hl2master.steampowered.com" call gethostbyname test eax, eax jnz legit_resolve ; If DNS fails, return static IP (127.0.0.1) mov eax, offset local_ip ret Keywords: DRM Circumvention, Source Engine, Video Game Preservation, Network Spoofing, Abandonware.
Half-life Deathmatch- Source Activation Crack -
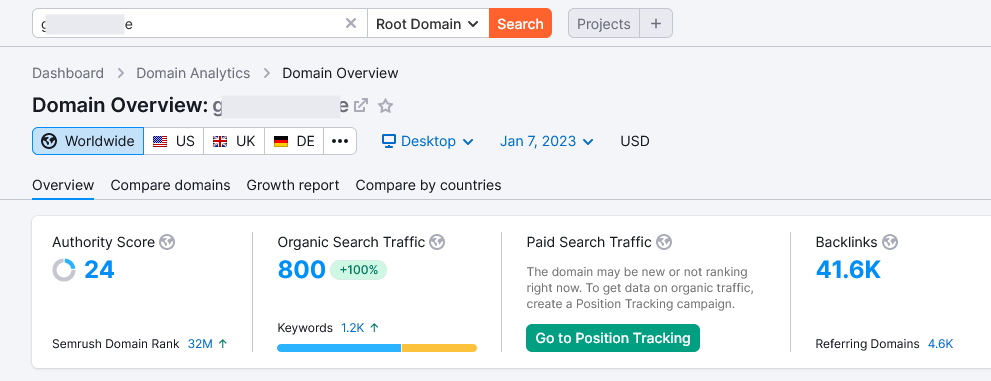
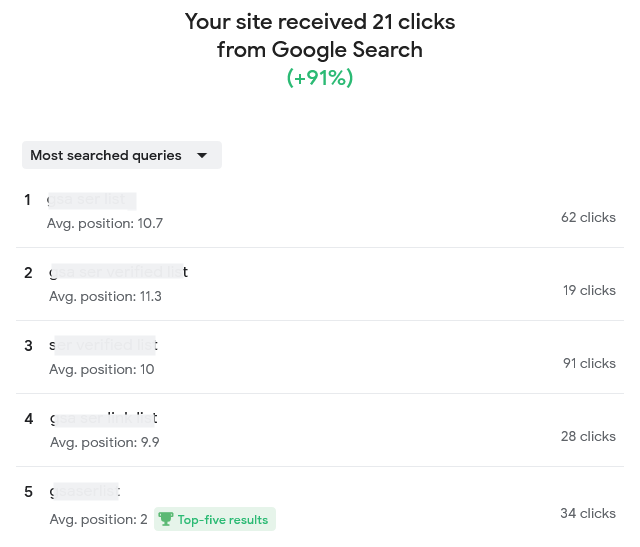
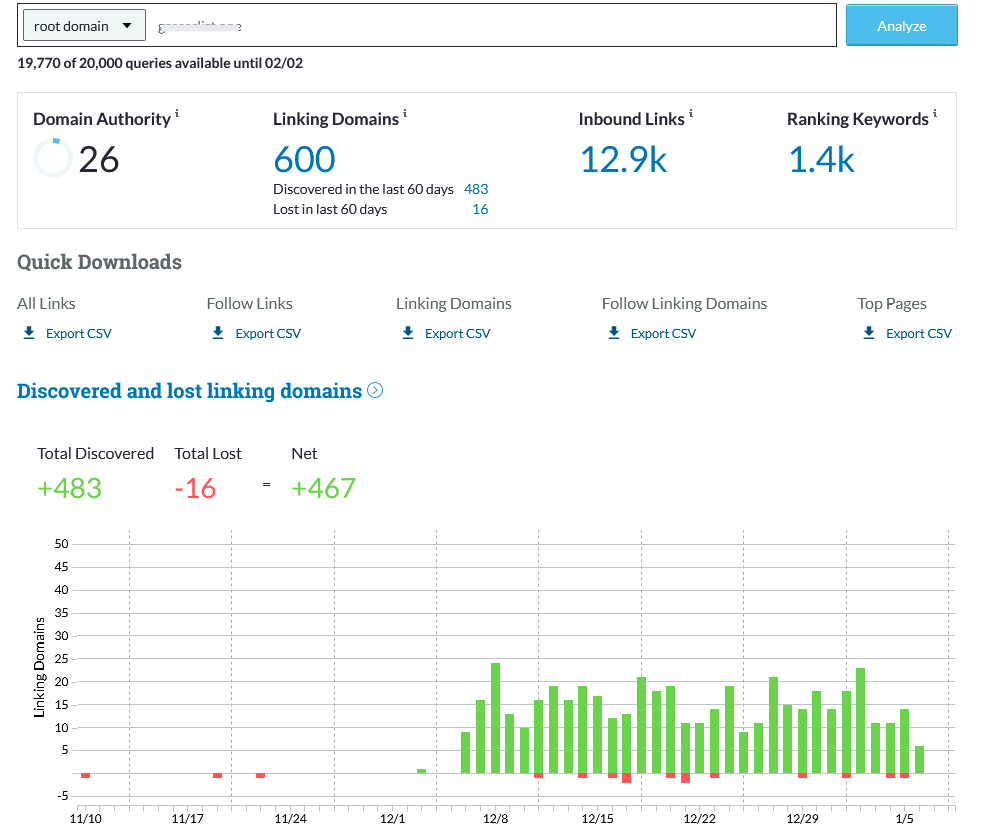
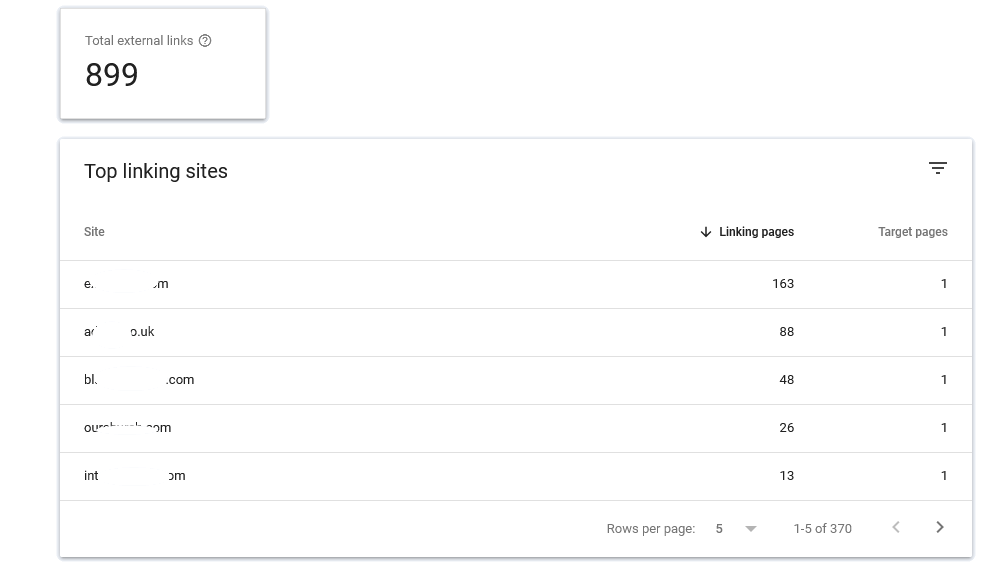
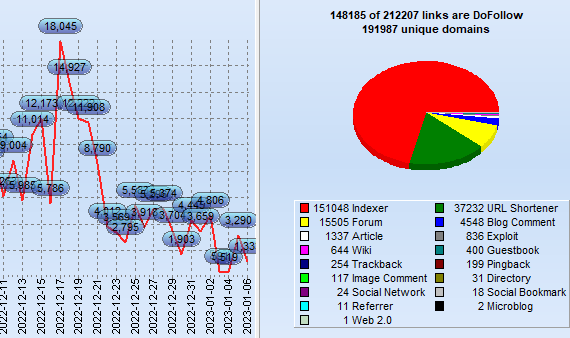
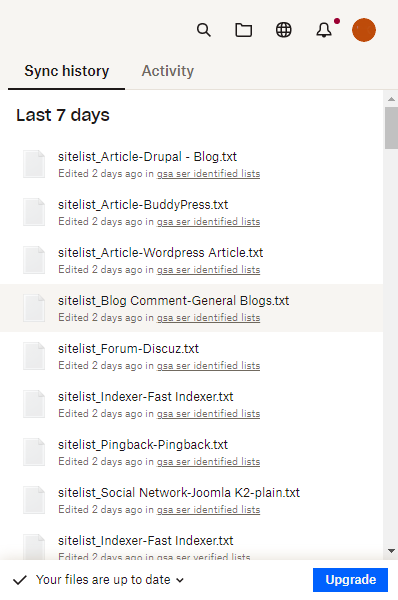
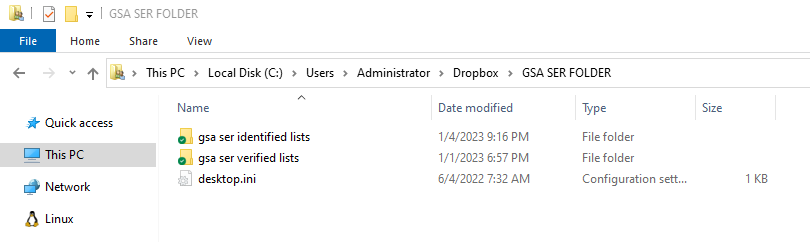
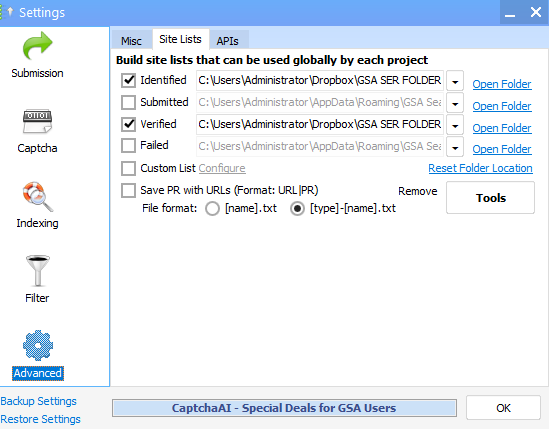
What exactly is GSA SER Verified List? And What is the best way to rank on It?
GSA Search Engine Ranker (SER) is an effective tool utilized by SEO professionals to create high-quality
link opportunity for their websites.
With GSA SER, marketers are able to quickly develop an inventory of verified hyperlinks that are
specifically tailored to the specific requirements of their clients. This allows them to concentrate on
those that are relevant and achieve the most effective outcomes.
Benefits of Using a GSA SER Verified List
The use of the GSA verified list for SER enables marketers to quickly and effortlessly identify top-quality
link building opportunities that can improve their rankings on search engine result page (SERPs).
Half-Life Deathmatch- Source Activation Crack
It is constantly updated continuously to ensure that marketers can be assured that they are receiving the
most recent information available. Furthermore, many of the websites listed on the list are from sites that
are low-OBL Tier 1 This means they are more likely to attract high traffic and aid your blog or website to
climb up the ranks.
How Do You Improve Your Ranking by using the help of a GSA Verified Lists of SERs?
Once you've found opportunities to build links from the GSA SER verified list, it's crucial to concentrate
on creating content of high quality that is engaging for users and ultimately get them clicking on your site
or blog.
More importantly, it proves a counterintuitive theorem of
Making informative, useful and relevant content can help you get higher rankings on the results pages of
search engines by demonstrating to Google that your website is an authority in the topic. It is also
important to ensure that all links link back to your site or blog, since this will provide Google the
impression of trustworthiness and relevancy when it comes to ranking.
What Are Some Best Practices When Using a GSA SER Verified List?
If you are using a GSA SER verified list, bear in your mind that when you are looking at link opportunities
for building quality must always take priority over the quantity. In addition, focusing on generating
articles that are valuable to users rather than trying to build the most links possible will ensure higher
rankings in the long run.
| | Ticket replay | Dynamic ticket nonces
Not last, you should be careful not to overuse keywords overly often to prevent your website from being
considered low-quality or spam and causing your rankings to drop instead of increasing.
Conclusion: SER Verified List
Utilizing the GSA SER list will offer SEO professionals with top-quality link
building options specifically to their requirements that can result in better rankings for their site or
blog over time, if followed correctly, following best practices, such by focusing on the creation of
high-quality content, not quantity, as well as avoiding keyword stuffing and so on.
In the end making use of this tool in the right way will allow you to achieve higher results in search
engine optimization more quickly than ever before!
Order Now
More importantly, it proves a counterintuitive theorem of digital security: The crack is frozen, self-contained, and asks for no permissions. The official client is a living binary that decays as Steam’s API updates.
| Crack Version | Valve Counter-Measure | What it Revealed | | :--- | :--- | :--- | | engine.dll patch | Steam’s “Ultrascope” CRC check on engine.dll | That client-side authority is a myth; server trust is all that matters. | | Ticket replay | Dynamic ticket nonces (timestamp checks) | That Steam tickets had no hardware binding until 2009. | | Listmaster spoof | Forced server-side challenge-response (2011 update) | That Valve assumed the master server was the single source of truth. |
Abstract This paper examines the socio-technical phenomenon known colloquially as the “Half-Life Deathmatch: Source (HL2:DM) Activation Crack.” Rather than a simple piece of piracy software, this artifact represents a unique intersection of digital rights management (DRM) history, network protocol manipulation, and post-hoc game preservation. By analyzing the executable patches released between 2006 and 2010, this paper argues that the HL2:DM crack is not merely a tool for theft but a “phantom protocol”—a reverse-engineered key that inadvertently documented the shift from optional CD keys to mandatory, always-online Steam authentication. 1. Introduction: The Orange Box’s Shadow Released in 2006, Half-Life 2: Deathmatch was more than a multiplayer shooter; it was a stress test for Valve’s Steamworks API. Unlike its predecessor (the original Half-Life Deathmatch ), HL2:DM had no offline mode. It required a persistent connection to Steam’s authentication servers to even launch. This created a digital ghost: millions of copies of the game existed on physical CDs (from The Orange Box or HL2 Silver/Gold packages), but the activation server was a live, mutable gatekeeper.
Ultimately, the HL2:DM crack is not a hacker’s triumph or a pirate’s shame. It is a —ugly, illegal, and absolutely necessary for the archaeological recovery of early 2000s Source Engine multiplayer.
; Redirect master server DNS push offset szHostname ; "hl2master.steampowered.com" call gethostbyname test eax, eax jnz legit_resolve ; If DNS fails, return static IP (127.0.0.1) mov eax, offset local_ip ret Keywords: DRM Circumvention, Source Engine, Video Game Preservation, Network Spoofing, Abandonware.